TL;DR: VT4Splunk, VirusTotal’s official Splunk plugin, correlates your telemetry with VirusTotal context to automate triage, expedite investigations and unearth threats dwelling undetected in your environment. This extends Splunk’s own VirusTotal plugin for their SOAR. Next March 30th we will host a webinar along with Splunk to show how to do security investigations with Splunk and VirusTotal. Register here!
One of VirusTotal’s main use cases is technology integrations, where VirusTotal’s context is used for automatic security telemetry enrichment, false positive discarding, 2nd opinion detection (true positive confirmation) and incident contextualization + investigation.
VirusTotal had Splunk plugins for a while, most of theme developed by community contributors and other 3rd-parties. For instance, VirusTotal’s plugin for Splunk SOAR, which ranks #1 in the Threat Intelligence Reputation space is developed by our friends over at Splunk, and we highly recommend it.
However, we wanted to truly showcase what VirusTotal can do for your SIEM and VT4Splunk v1 is our proposed solutions. It is free and you can download it from Splunkbase. It is compatible with Splunk +8.x Enterprise and Cloud versions.In a nutshell, VT4Splunk automatically enriches your Splunk logs with threat intelligence coming from VirusTotal, to gain superior visibility and understanding. Let’s dive into specific use cases and outcomes.
Expedite triage and investigations via on-demand command-line driven enrichment
When studying an alert or incident, analysts often need to sweep through hundreds or thousands of events to make sense of an attack. Narrowing down massive amounts of events to focus on those that are relevant in the context of an attack is complex and time consuming.
VT4Splunk adds a command to trigger correlation of events with threat intelligence (reputation and context) from VirusTotal, which in turn allows you to perform subsequent filtering to focus on events that look particularly anomalous.
The "vt4splunk" command initiates the enrichment, it can be appended to any Splunk SPL query. For example, let's say you have run a query that returns all events related to a specific IP address. To enrich resulting events with information from VirusTotal, simply append the "vt4splunk" command to the query:
index=myindex sourcetype="stream:http" | vt4splunk ip=dest_ip
VT4Splunk will automatically retrieve information from VirusTotal for each IP address returned in the query results. This information includes the number of malicious detections, the first and last seen dates, and most importantly, context and analysis properties that can be used for triage and hunt missions:
This also applies to other observable types, such as file searches. The following example search enriches hashes found in Sysmon events:
| vt4splunk hash=SHA256
The correlation is made via VirusTotal’s API and, thus, also understands domains and URLs found in events, beyond file hashes and IP addresses.
Make better decisions and minimize missed threats with IoC contextualization via the VT Augment widget
Security teams are increasingly concerned about missed threats due to lack of context. Indeed, the use of reactive threat feeds, the adoption of ML and generic detections, the popularization of anomaly based detections and UEBA, etc. is leading to alerts where there is extensive context about the internal systems where a given anomaly was observed, but little context about the threat itself. This means that it is easy for analysts to discard true positives.
VT4Splunk incorporates hooks throughout the Splunk interface to open up full-blown VirusTotal reports:
But most importantly, it also introduces triggers to open up the VT AUGMENT widget within Splunk, in a single pane of glass fashion, for all IoCs that get highlighted in dashboards and reporting views:
These Crowdsourced Intelligence cards do not only provide a detection 2nd opinion but also in-depth static, dynamic, code and threat graph analysis allowing analysts to make faster and more accurate decisions. Moreover, when available, the embedded report will add a layer of attribution describing campaigns, malware toolkits and threat actors tied to a given flagged IoC.
Automatically prioritize threats with enrichment and triage via scheduled queries
The aforementioned command-line driven enrichment can actually be automated in the plugin’s configuration (Correlation Settings).
Upon doing so, any notable findings (flagged files, domains, IPs or URLs) will be called out in the Threat Intelligence view, which is both a dashboard and reporting vehicle summarizing malicious activity seen in your environment:
The flagged IoCs are contextualized with relevant data points such as the threat family or category, and upon clicking on them a table opens up with all events in which the pertinent IoC was seen, which tremendously expedites investigations.
Reduce exploitation risk by prioritizing patch application
The Vulnerability Intelligence view is also populated with correlations coming from automatic enrichment. It allows SOC teams to implement vulnerability prioritization. Some logs that are dumped into Splunk come from email gateways, firewalls and other solutions that have network perimeter visibility. These logs are a good reflection of what an organization’s threat landscape is, even when a security solution has stopped a threat, fully tailored intelligence can be derived from them.
Files submitted to VirusTotal are tagged with any CVEs for vulnerabilities that they might be exploiting. This means that VirusTotal allows you to understand which vulnerabilities are truly being abused in-the-wild by attackers as opposed to those for which there is only proof of concepts.
Security teams often prioritize vulnerabilities based on their severity as reflected in the generic vulnerability report. This is suboptimal, it fully ignores whether the vulnerability is being actively exploited and whether you are actually being hit by exploits targeting it.
VT4Splunk runs through all your events, extracts hashes seen in them, identifies those that are tagged in VirusTotal with CVEs and summarizes the findings in the Vulnerability Intelligence view. This allows you to implement a tailored vulnerability management strategy that represents the intersection of your organization’s threat landscape and in-the-wild exploitation.
Again, clicking on any of the highlighted CVEs will open up a table listing all those files seen in your environment and abusing the pertinent vulnerability, and all those events in which those hashes were seen.
Identify threats dwelling undetected in your environment with Adversary Intelligence
VirusTotal is the richest and most actionable Crowdsourced Threat Intelligence suite, as such, its firehose of threats and sightings is often overwhelming. Security teams need to focus on what’s truly relevant for them and often prioritize incident response and threat handling based on the threat actors behind them.
We recently rolled out threat {campaign, toolkit, actor} cards in VT ENTERPRISE. These reports summarize threat campaigns/actors, their motivations, targeted industries, source regions, etc. They also provide actionable intelligence such as related IoCs, TTPs, in-the-wild geo+time activity telemetry, {YARA, Sigma, IDS} rules to detect them, online reporting, etc.
If your account has access to the aforementioned Threat Landscape module, VT4Splunk will also populate an “Adversary Intelligence” view flagging any campaigns/toolkit or actors seen in your environment:
Yet again, upon clicking on an identified campaign/toolkit or actor, the associated IoCs and events in which they are contained will open up. This allows security teams to focus on more severe threats first as opposed to script kiddies, mass malware or generic ecrime.
Similarly, all of the flagged items have a shortcut to jump into VirusTotal’s report about the given campaign/toolkit/actor, where you can continue to investigate and dive into things such as their geographical and time-based activity:
What’s coming next?
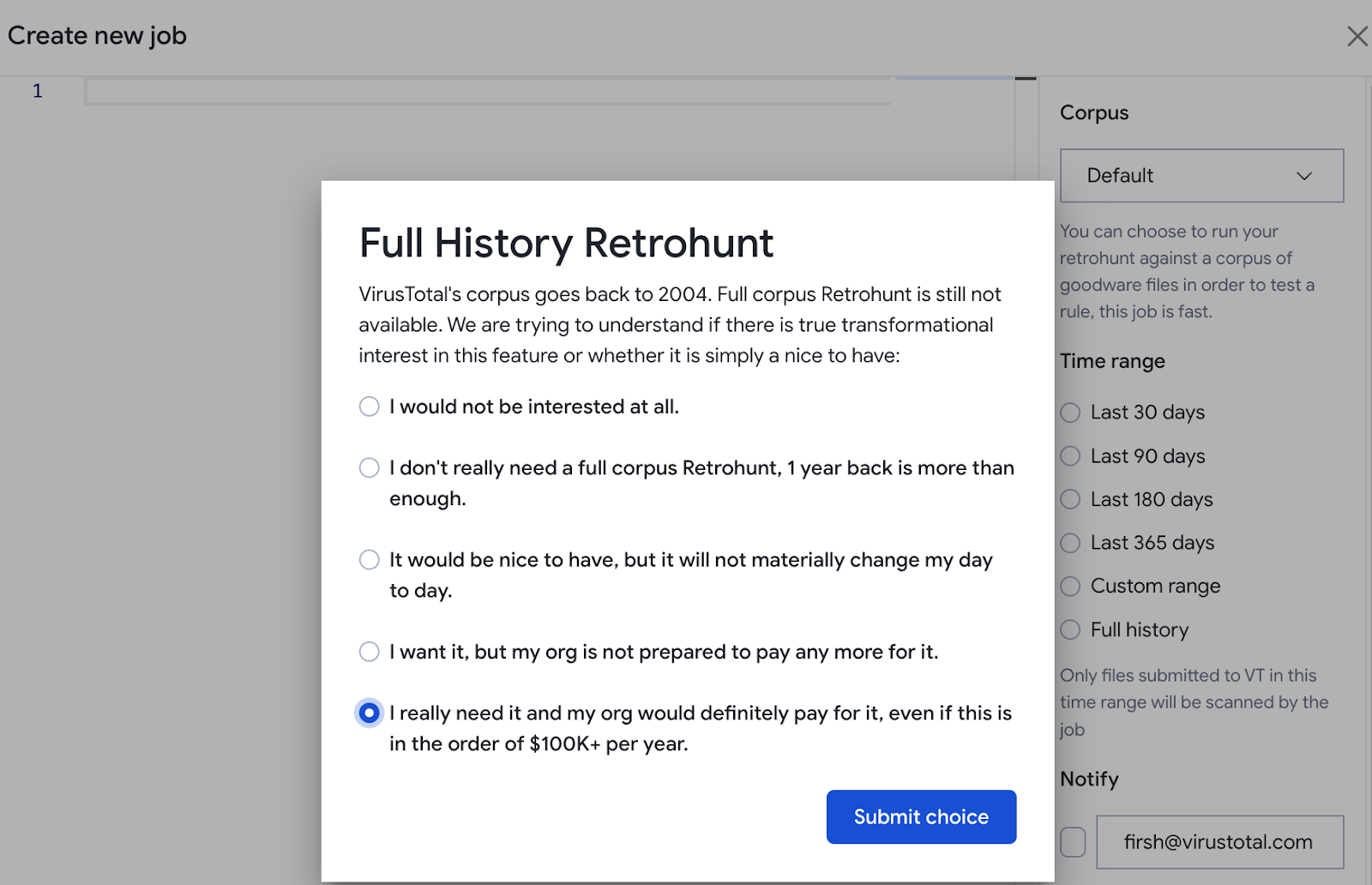
This is by no means the end of the road for VT4Splunk, we have many features in the making. Over the coming months, among other things, we will:
Add a MITRE ATT&CK view summarizing TTPs seen in your environment, through the dynamic analysis to MITRE ATT&CK mappings that VirusTotal sandboxes perform.
Incorporate a tab summarizing adversary TTPs into the Adversary Intelligence view, providing a more focused understanding of the modus operandi of identified actors in particular.
Democratize threat hunting with one-click canned hunts that will act on the correlation of your events with VirusTotal analysis metadata and relationships.
Enhance detection with tailored threat feeds based on subscriptions to specific threat campaign/toolkit/actor cards, Livehunts and scheduled VT Intelligence queries.
Implement multi-layered detection by allowing users to apply crowdsourced Sigma rules from VirusTotal to their own telemetry, acting as event based/behavioral pattern detection and thus complementing the rest of their security stack.
Please do not hesitate to join us next March 30th, when we will host along with Splunk a webinar to show how to do security investigations with Splunk and VirusTotal. Register here!
Happy hunting!