We recently conducted our first “Threat Hunting with VirusTotal” open training session, providing some ideas on how to use VT Intelligence to hunt for in-the-wild examples of modern malware and infamous APT campaigns. In case you missed it, here you can find
of the slides with all the queries covered during the session and direct links to the documentation.
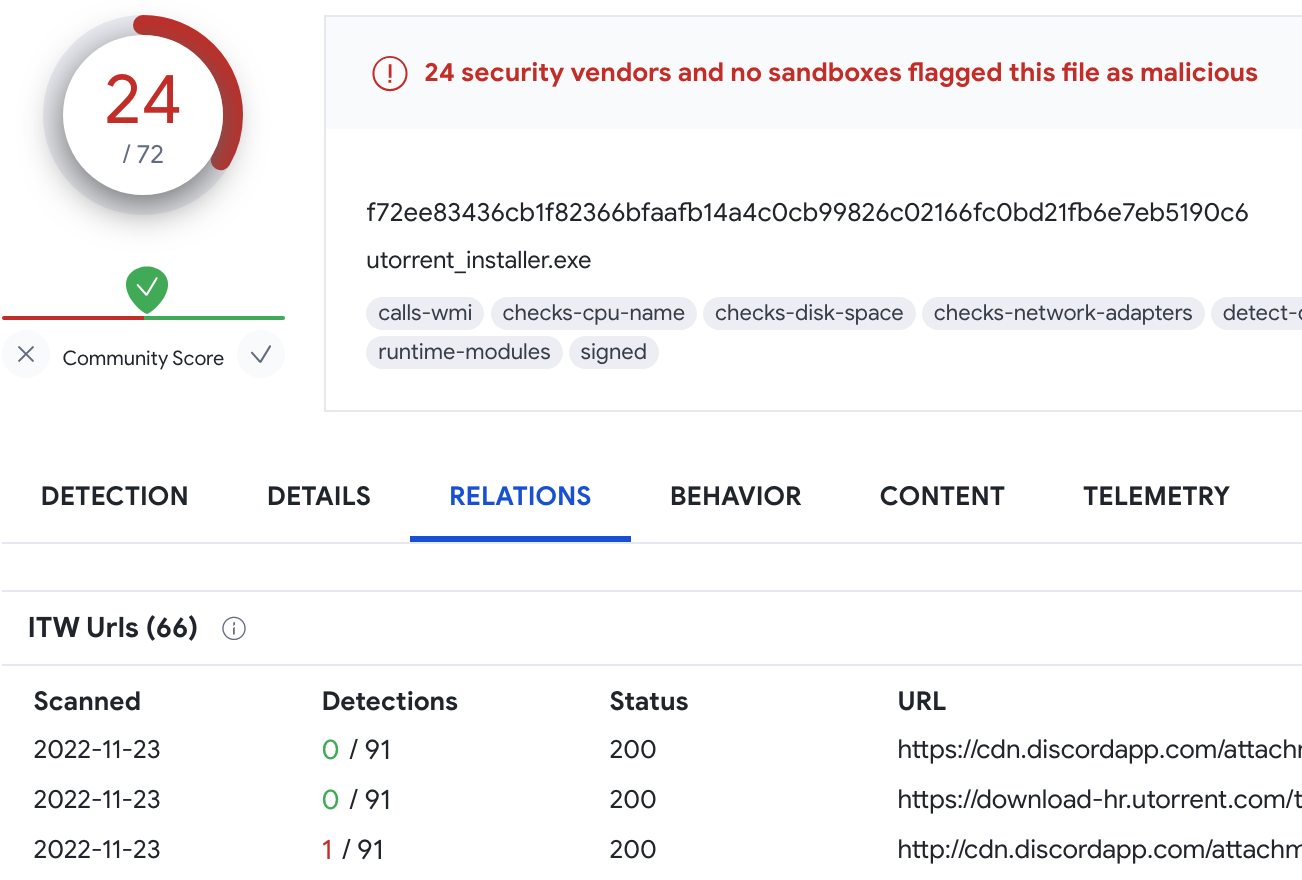
1. How can we search for “have:itw” with a specific URL?
“have:itw” is a search modifier you can include in your VT Intelligence queries to get all samples we found being distributed in the wild. You can specify any particular domain in your query, for instance the following example finds samples being distributed itw through discord:
2. How can we convert the search queries to monitoring alerts?
Good question, at the moment we are working on a solution to do this automatically, hopefully available very soon. In the meantime, there are two workarounds: execute your query through the
API or, in some file-related cases, you can rely on the
Yara VT module to create and deploy a
Livehunt rule.
3. Is there any documentation on the VT website for all this info?
4. Can we have sessions on hunting part of VT like this.
Yes, we will be having quarterly “Hunting with VT” sessions (at a minimum).
5. Can we use regex in queries?
There are no wildcards for most of the regular VT Intelligence queries with the exceptions of “name:” and “domain_regex:”, because we use full text search. In some cases you can achieve the same effect by combining search terms with the “AND” keyword.
6. Can you point out a location for all the most useful queries?
We are working on a Cheat Sheet which will be available very soon, stay tuned.
7. Can you see the content tab in the free version?
This is only available to VT Enterprise customers.
8. Can you use wildcards in date notations when searching?
Date notations are quite flexible even without wildcards. For example, for malware submitted to VT in January this year you can use the following:
You can get malware submitted for the last 5 days with the following query:
9. What is your keyboard? Super nice sound.
DROP CTRL + Kaihua Speed Silver + T0mb3ry SA Carbon
10. Does “crowdsourced...:malware_name” will give all the rules sigma/yara written for that malware?
Not really. Rules are not assigned to any malware or actor in particular, so we need to rely on the name of the rule. For instance:
provides you with files detected by the Yara or IDS rules with “Sofacy” in its name.
11. Does Virustotal collect samples from sources other than user submitted files? For example, does it passively scrape the Android App store to check for new apps created by APTs?
Yes! Just as an example, you can submit a file to VirusTotal from Process Explorer. Also, there are different research groups and other volunteers (thanks again to all of you!) who share new samples with the VT community.
12. How to fetch all the matched samples for a query by script instead of going through all pages?
13. Sometimes I tried to perform behavior search using powershell commands, but it doesn’t work for me. For example, this one. When clicking to the powershell command itself, returns no results. Also, doing something like behavior:"PAAjAGcAeABwACMAPgAgAFIAZQBnAGkAcwB" does not work. Thanks for the heads up! There is an issue when transforming super-long strings into a search query, we are already working on a fix.
Regarding the second question, when doing a full text search unfortunately it is not possible to use substrings (unless it is a separate word). For example:
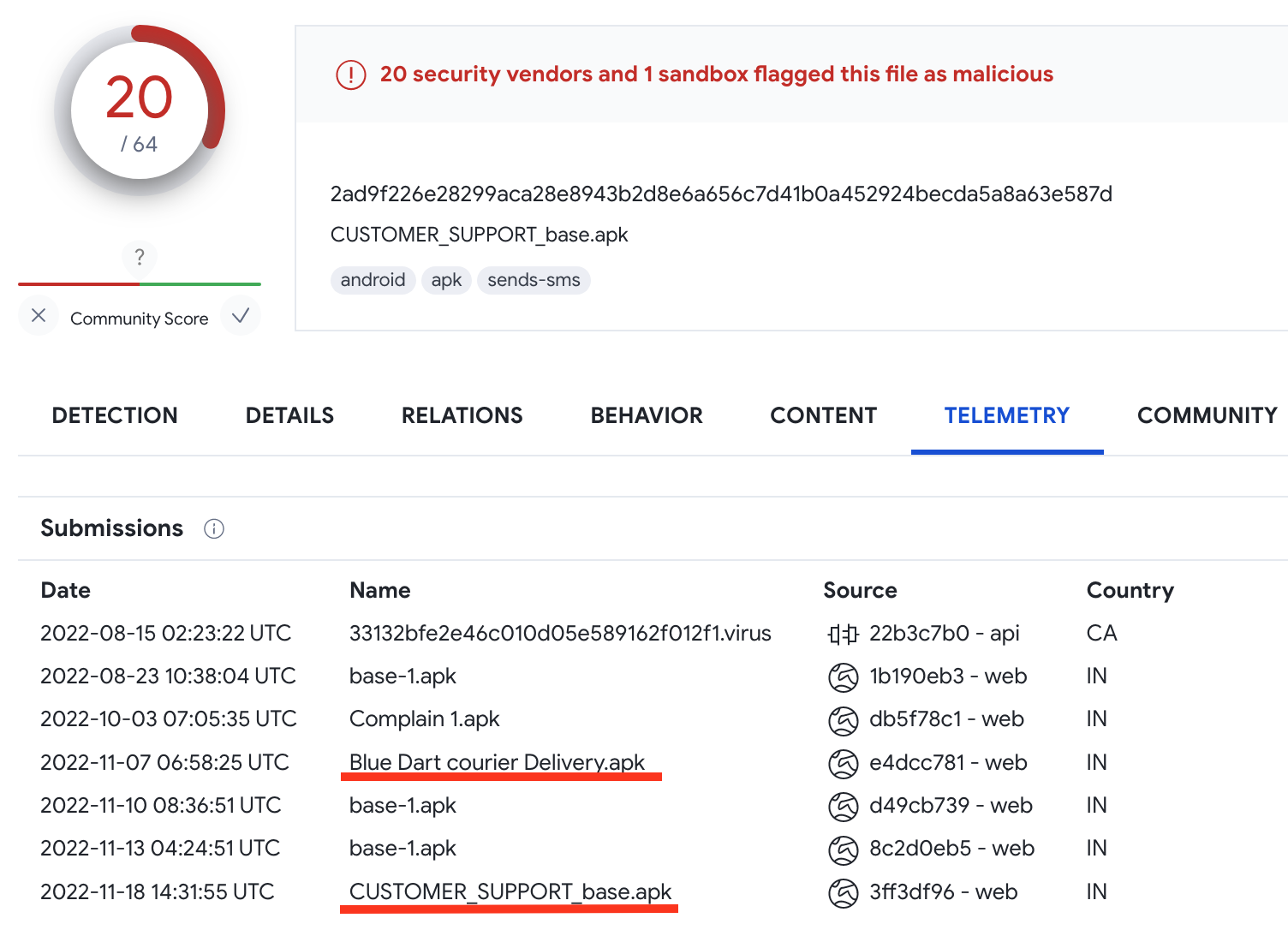
Searching for the initial infection vector is tricky and not always possible as it depends on VirusTotal’s visibility, but you can try the following ideas:
15. Do you have a link to all available VT "entity:" types?
That would be “file”, “url”, “ip”, “domain” and “collection”. You can find extensive information with documentation links on the slide #5 of
PDF slides. This will also be available soon in
VirusTotal’s documentation.
16. How can we utilize the VT API to upload our own PE files to sandboxes for dynamic analysis? I have been running it on some executables and most of the files error out during the sandbox execution (e.g. tries to open a file in the file system that doesn’t exist, etc).
Sandboxing is part of the executable processing pipeline, you can submit your files using
this API endpoint. Regarding any technical issues including unexpected sandboxing behavior you can reach out to Virustotal Bot at the bottom of the website.
Thanks for your request, we’ll think about how to make the Yara editor pleasant for everybody.
18. Can you show an example of using language with word document search? How can I search for Follina samples with specific languages?
The “lang:” keyword finds all files whose Exif language property matches the language provided. In Follina case, following our training instructions, we can use the crowdsourced Yara rule with language clarification:
19. Is there a thinking on future development for GodMode to be able to label deployed malwares by sectors? like Healthcare?
20. Is there Mitre Attack type T. identifier search?
Yes, you can use the following keywords and specify any technique or tactic.
21. Is there a way to run custom tools on top of what is available?
You can always organize a custom post-processing of VirusTotal data by using our
API. This is exactly what the “APT dashboard” we showed during the training does.
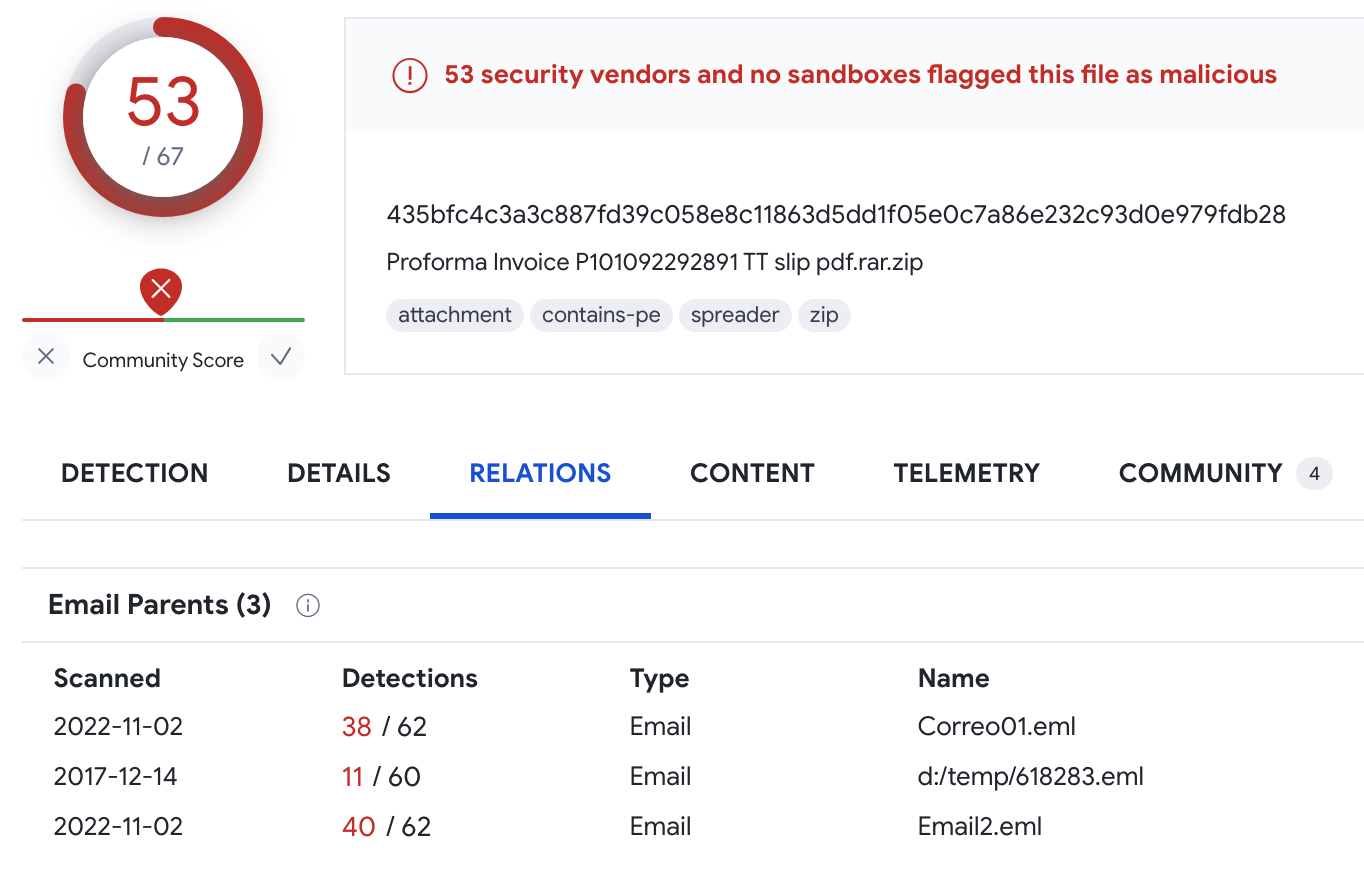
22. Were we able to search for a specific email and see all other files distributed by the email?
You can leverage VT Grep to search for email files with specific content and then pivot to the children entities as it appears under the Relationship tab, for example:
23. How can we combine a domain and a file seen together?
If you want to get files downloaded from a specific domain (drive.google.com in the example below), you can use:
24. What about wildcards in androguard on receivers/services/activities?
Unfortunately, this data is indexed as full-text search, so no wildcards are allowed. However, if you feel that this is critical to you, please feel free
to reach out.
25. What encodings are accepted by the "content" query parameter? Is it only plaintext and hexadecimal?
26. Why isn't it possible to combine the "have" and "content" modifiers? I have the following error: "have can't be combined with content modifier", example: have:email_parents AND content:"Hello World!"
Content search is a different querying tool by design, that's why it is not possible to combine with all the other keywords by default. We are collecting the feedback and adding compatibility with the most popular ones (tag, type, p, fs, etc). For more details please refer to
VT Grep documentation.
27. How can I submit a yara or a sigma rule to VT for community use? Are they generally just obtained from curated open source?
Yes, we are always looking for solid and active repositories constantly updated with the latest malware signatures. You can find the number of such repositories in our
Contributors list. If you do want to contribute, please let us know.
28. Will the APT dashboard be downloadable from GitHub? Would it be possible to share one of your jupyter notebooks, please?
At the moment we are not openly sharing such notebooks, which are mostly designed for demoing and internal research, and we are not really sure if they are solid enough for production environments. We are currently studying if this is something we will be doing in the near future. However, we are happy to help you build your own! Please feel free to let us know in case you are interested in this or any other ideas.
If you have any other questions, please feel free to
reach out.
Happy hunting!