Malicious activity comes in all kinds of colors and flavors, sometimes abusing users’ trust by impersonating well known brands to get their private data, install malware or any other form of scam. At VirusTotal we analyze more than 3 million distinct URLs daily obtaining not only AV verdicts from more than 70 different vendors but also extracting as much data as possible including headers, cookies and HTML meta tags. This data is indexed and related to other observables we keep in our database, which is an excellent way to track malware infrastructure but also to find other forms of fraudulent activity. Indeed, many of our customers use VirusTotal daily to monitor brand abuse and fraudulent impersonation.
In this post we will describe how VirusTotal served to investigate the Anniversary brand abuse campaign by our good friends from Hispasec.
How to start our investigation
In this particular case, the campaign was distributed mostly using WhatsApp messages, where the victims were encouraged to share with their contacts links similar to the following ones:
hxxp://luby3a0[.]cn/r2eizhga/adidas-mo
These domains seem to be randomly generated. Now, starting from this information, how can we start an investigation in VirusTotal? There are a few handy VTI modifiers we can leverage:
Tracker: Many websites use different ads trackers, which we will try to find inside the HTML body of the analyzed URL. If two websites share the same ad tracker, it usually means they’re owned by the same person. You can use this modifier to find URLs where we found the same tracker. Example VTI search: entity:url tracker:G-J151F98PH2
Title: The title of the website as contained in the HTML response. Example VTI search: entity:url title:"🎉Adidas 70th Anniversary!🎊"
Path: Will find for us URLs containing a string in particular. Example VTI search: entity:url path:adidas-mo
Main_icon_dhash: Here we will find other websites having the same favicon. In this case, VirusTotal will calculate the favicon’s hash for us and do a fuzzy search to find similar ones. Example VTI search: entity:url main_icon_dhash:4932332b178e4d20
Response_sha256: This is the hash of the response we obtained when visiting a website. Example VTI search: entity:url response_sha256: e839c5398c1fe08dde3a4b0ffb39fd6b6a7c6dcab9d5477b0dfdfe8d62bcd77b
It seems we have several ideas to start our search with. As you have probably already realized, values used in the previous example VTI searches correspond to the two malicious websites we started our analysis with. Some of them are extremely precise for a given search (such as the response sha256), while others, like the favicon, title and path look interesting for any automatically generated infrastructure. However one of the key elements for this investigation was the tracker, as it identifies the website owner.
Let’s first check the prevalence of all these different elements among VirusTotal:
The number of found items is pretty high, which could either mean this is a large campaign or the values are not really representative. Combining three of the criteria listed above (title, tracker and path) in a single search returns 13.86K results, confirming it is a huge campaign. We can add some extra modifier like p:5+ (detected as malicious by at least 5 different AV vendors) for a total of 11.02K, confirming our suspicions.
Leveraging VT Graph
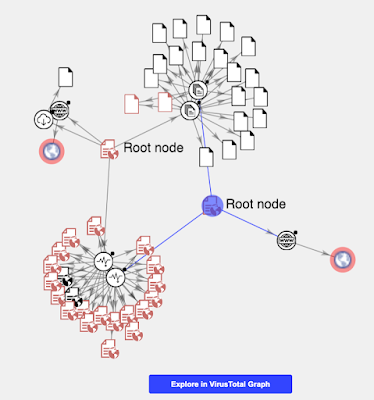
Another way to start our investigation would be taking advantage of VT Graph. This would put on the table all the elements related to the IOCs we have to start our investigation with, giving us a good idea of the dimension and of the elements of interest.
The graph helps us visualize what both URLs share in common, as well as a bunch of additional ones that also share the same tracker ID. In particular, there are a couple of common javascript libraries detected as malicious by several AV vendors that look interesting for our investigation. We can open their VirusTotal report in the links below:
We don’t need to download any of these files to analyze them, as happily VirusTotal allows us to check their content at the content tab in the file’s report.
Indeed, when doing that there are several very significant strings that seem highly related to the campaign we are investigating, such as “var project = "adidas-mo";”. We can simply click on this string to find any other files that include the very same content:
This results in hundreds of libraries that were used by attackers, most likely in this very same campaign. Displaying a LARGE number of elements in a graph is probably not the best idea, but nevertheless this is how it looks like:
This gives us a very quick idea on how clustered this campaign is. We can pivot all this data to obtain the full infrastructure used in the campaign. For large automated processes like this one, we also recommend using our API or vt-client.
It all started with a couple of URLs
Having a large malware database creating relationships among all indicators and allowing pivots using any of them has its advantages. You never know what is the particular criteria that would be the key element for a particular investigation, in this case both “tracker” and “path” proved to be very useful. Visualizing information is also one of the most powerful methods to quickly understand what is most relevant from the data you are working with, allowing you to quickly focus on the most important elements.
Both methods shown in this post are some ideas to use when tracking brandjacking or any other fraudulent activity, if you have any other favorite methods you use for your investigations and you want to share with us please do not hesitate to contact us.
Happy hunting!


0 comments:
Post a Comment