YARA rules are an essential tool for detecting and classifying malware, and they are one of VirusTotal’s cornerstones. Other than using your own rules for Livehunts and Retrohunts, in VirusTotal we import a number of selected crowdsourced rules provided by contributors to help identify and classify samples (example report). However, finding, tracking and managing VirusTotal’s crowdsourced YARA rules can be challenging, especially as the number of rules and contributors grow. To address this, we introduce the new VirusTotal’s Crowdsourced YARA Hub, allowing users to easily search and filter existing rules, track new ones and one-click export any of them to Livehunt and Retrohunt.
It is important to highlight that the Crowdsourced YARA hub does NOT include your private VirusTotal Livehunt/Retrohunt rulesets, it rather centralizes all contributor/community YARA rules that are currently contextualizing files submitted to VirusTotal.
The new Crowdsourced YARA Hub can be found under “Livehunt”.
The new repository makes it easy to find existing YARA rules. Users can filter rules based on different criteria such as when the rules were created, who authored them, number of matches and threat category (based on the top threat categories in the samples matching the rule), in addition to search rules by name, description or metadata. This helps users quickly find the rules they need and avoid duplicating efforts. For example, let’s find all rules whose description, fields or title contain the word ransomware:
https://www.virustotal.com/gui/crowdsourced-yara-hub?filter=%22ransomware%22
This makes it way easier for VirusTotal’s users monitoring new rules for particular actors or campaigns, checking if any rule of our interest gets updated and being on top of fresh rules. Additionally, visualizing the number of matches also helps understanding the prevalence of given rules and calibrating its impact when we find matching samples during our investigations.
Moreover, it is also a vehicle to stay up-to-date with emerging threats identified by the community.
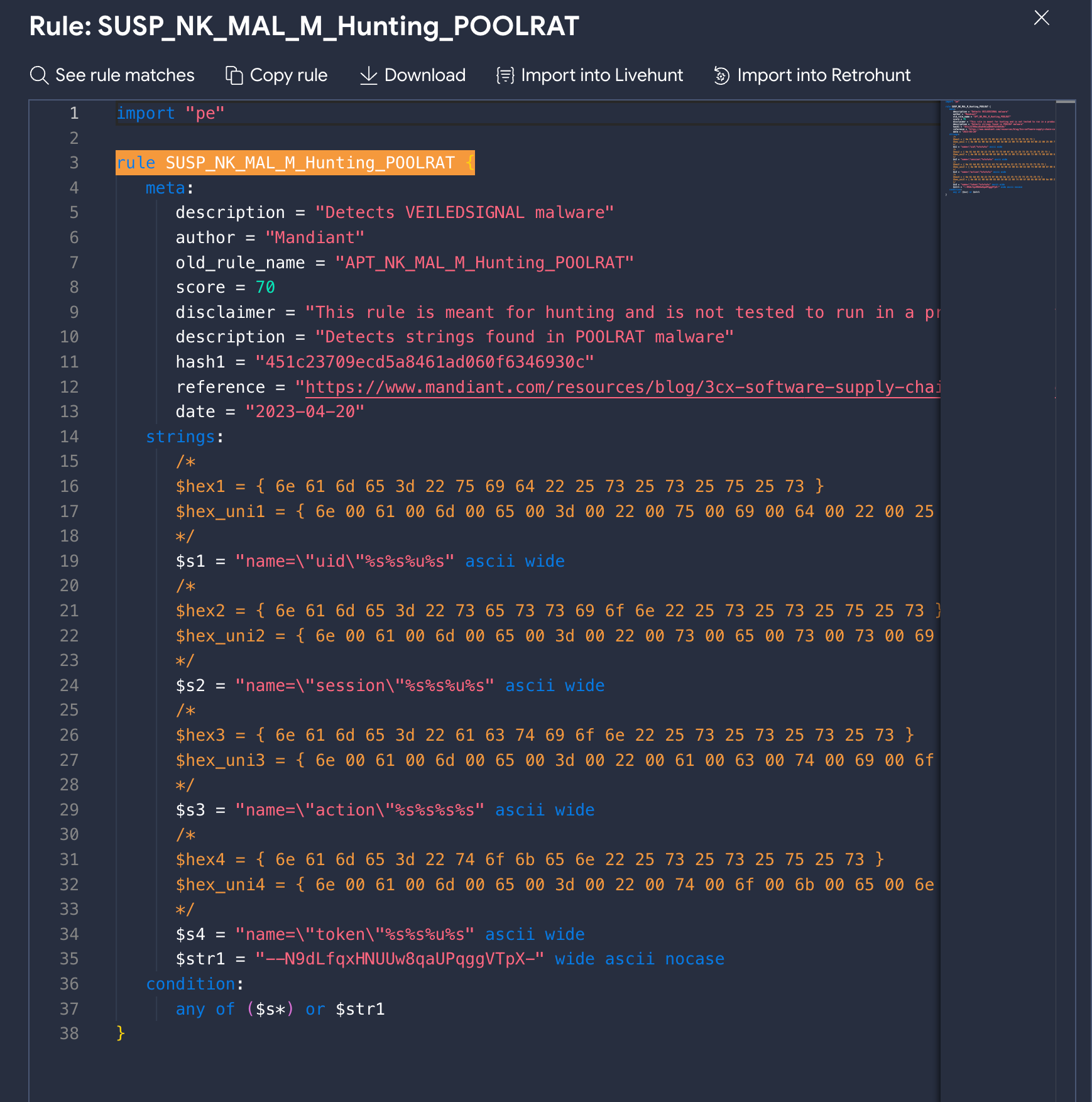
Additionally, the new central repository allows users to check and import YARA rules into other pipelines easily. You can visualize, copy, download and one-click import rules into Livehunt and Retrohunt. Downloading and exporting allows you to action the rule against your environment via your EDR or forensics tools with YARA support. As usual, you can check all matches for a given rule.
Did you notice how gorgeous YARA rules look in our new YARA editor? This is just a sneak peek of a very basic version and we will be providing more details very soon, but get ready for a YARA editor on steroids!
Conclusion
The new Crowdsourced YARA Hub provides many advantages that will help all VirusTotal’s users get familiar with and leverage crowdsourced YARA rules. Now it should be way easier finding rules of our interest, filtering out noisy rules from our analysis and focusing on the interesting ones and understanding what new rules are available to us to track actors and campaigns, all in a new interface that makes it easier to visualize them and one-click import rules into any pipeline. We encourage all our users to give it a try and share with us any feedback, and all YARA rules creators to let us know if you are interested in sharing your amazing rules with the VirusTotal community.
Happy hunting!





0 comments:
Post a Comment