Complementary threat context
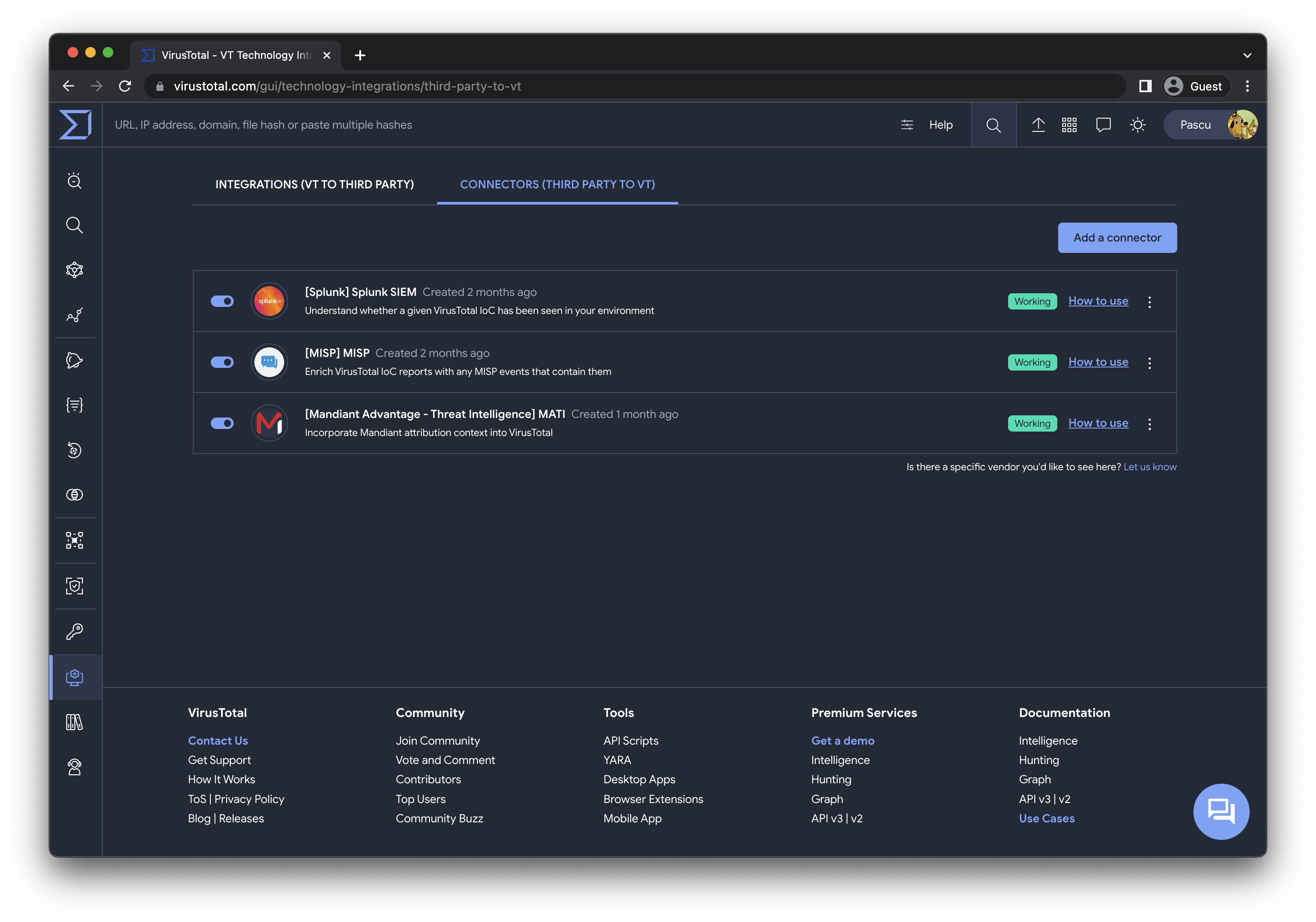
While this post doesn't delve into specific third-party connectors, we're excited to announce that Mandiant is among our first supported connectors. More details about this will be covered in an upcoming blog post.
In addition to Mandiant, we are introducing two other connectors, each offering distinct context for different use cases, provided by leading security providers:
-
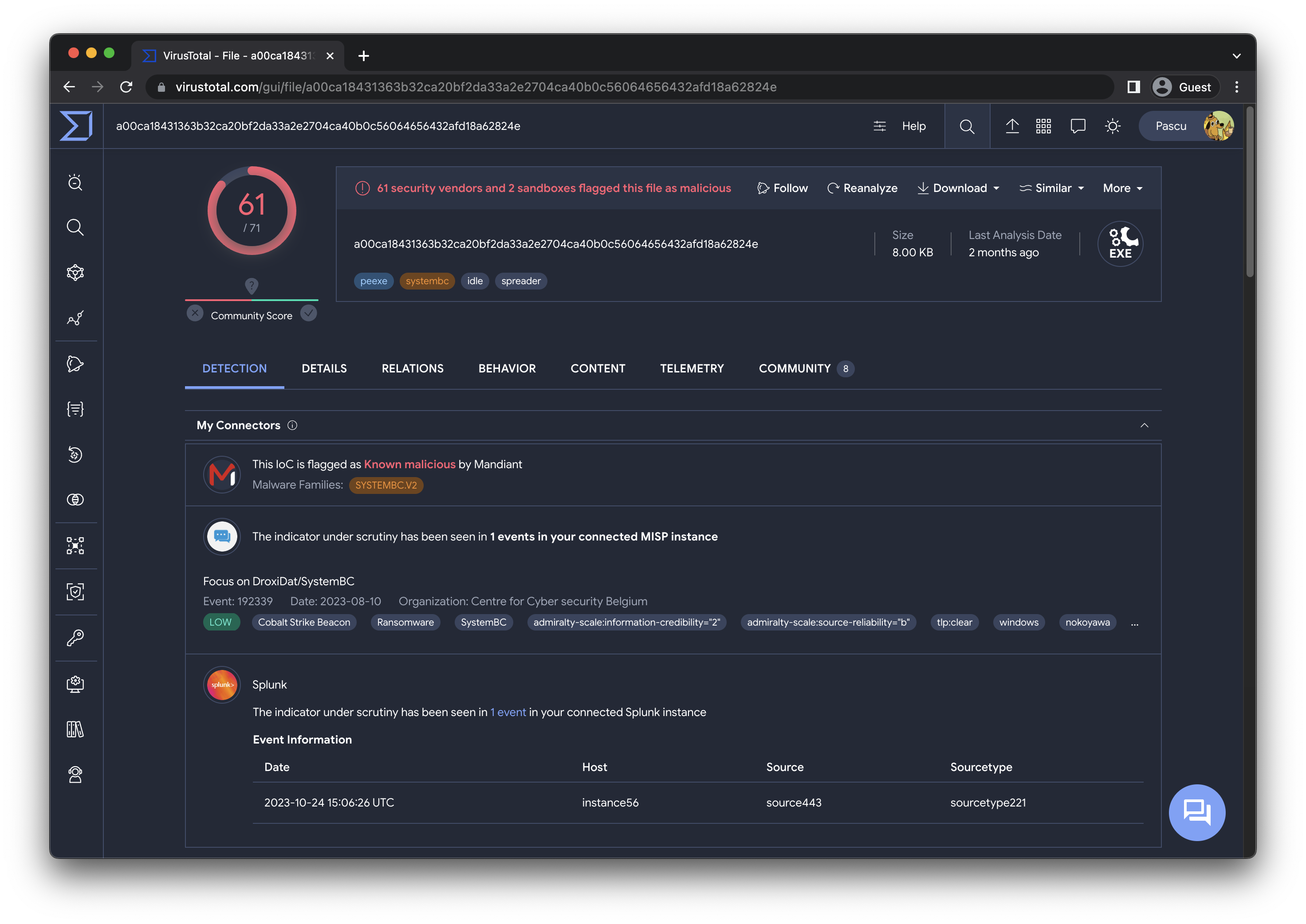
Mandiant Intelligence - This connector allows you to incorporate Mandiant's malware toolkit, campaign insights, and threat actor attributions into VirusTotal. Learn more.
-
MISP - Enhance VirusTotal indicator of compromise reports with information from MISP events, including descriptions, tags, and other pertinent data generated by your Cyber Threat Intelligence (CTI) team and trusted circles. Learn more.
- Splunk - Gain immediate insight into whether a specific VirusTotal IoC has been detected in your environment, either presently or in the past. Learn more.
Configuration made easy
Community development
Our journey doesn't stop here. We're already in the process of supporting more data providers. At VirusTotal, we firmly believe in the power of community collaboration. We're contemplating the release of a framework that empowers our community and third-party providers to create and contribute their own connectors, embodying our commitment to crowdsourced security.



0 comments:
Post a Comment